The data link protocols operate in the data link layer of the Open System Interconnections (OSI) model, just above the physical layer.
The services provided by the data link protocols may be any of the following −
The services provided by the data link protocols may be any of the following −
- Framing − The stream of bits from the physical layer are divided into data frames whose size ranges from a few hundred to a few thousand bytes. These frames are distributed to different systems, by adding a header to the frame containing the address of the sender and the receiver.
- Flow Control − Through flow control techniques, data is transmitted in such a way so that a fast sender does not drown a slow receiver.
- Error Detection and/or Correction − These are techniques of detecting and correcting data frames that have been corrupted or lost during transmission.
- Multipoint transmission − Access to shared channels and multiple points are regulated in case of broadcasting and LANs.
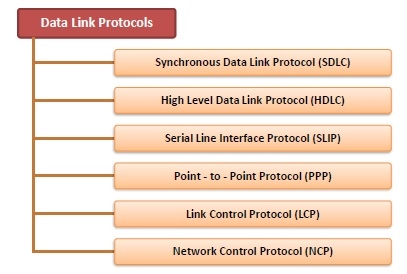
Common Data Link Protocols
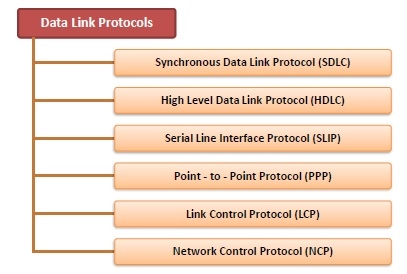
- Synchronous Data Link Protocol (SDLC) − SDLC was developed by IBM in the 1970s as part of Systems Network Architecture. It was used to connect remote devices to mainframe computers. It ascertained that data units arrive correctly and with right flow from one network point to the next.
- High Level Data Link Protocol (HDLC) − HDLC is based upon SDLC and provides both unreliable service and reliable service. It is a bit – oriented protocol that is applicable for both point – to – point and multipoint communications.
- Serial Line Interface Protocol (SLIP) − This is a simple protocol for transmitting data units between an Internet service provider (ISP) and home user over a dial-up link. It does not provide error detection / correction facilities.
- Point - to - Point Protocol (PPP) − This is used to transmit multiprotocol data between two directly connected (point-to-point) computers. It is a byte – oriented protocol that is widely used in broadband communications having heavy loads and high speeds.
- Link Control Protocol (LCP) − It one of PPP protocols that is responsible for establishing, configuring, testing, maintaining and terminating links for transmission. It also imparts negotiation for set up of options and use of features by the two endpoints of the links.
- Network Control Protocol (NCP) − These protocols are used for negotiating the parameters and facilities for the network layer. For every higher-layer protocol supported by PPP, one NCP is there.
Comments
Post a Comment